You’ve seen previous posts here about open source and open standards. Now its time to add open APIs to the mix. More specifically, openVuln, an API for immediate and programmatic access to critical security vulnerability information in a number of standard formats.
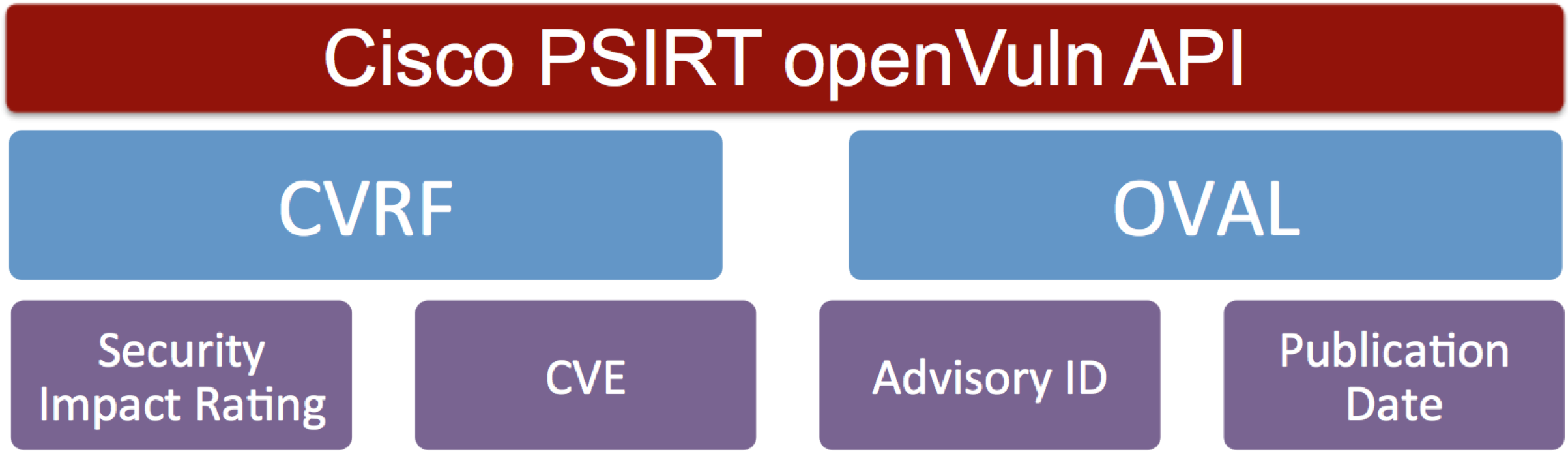
The Cisco Product Security Incident Response Team (PSIRT) recently released the openVuln API, a RESTful API that supports industry wide security standards such as the Common Vulnerability Reporting Framework (CVRF), Open Vulnerability and Assessment Language (OVAL), Common Vulnerability and Exposure (CVE) identifiers, and the Common Vulnerability Scoring System (CVSS). The openVuln API make it possible to build automated tools to deal with security vulnerability more quickly and effectively.
Automation is a hot topic in general these days, and security is no exception. Most organizations have many systems to patch and configure securely, with numerous versions of software and features enabled. Security administrators are seeking ways to leverage standards and available tools to reduce the complexity and time necessary to respond to security advisories, assess their devices, and ensure compliance so they can allocate resources to focus on other areas of their network and security infrastructure. The openVuln API addresses these needs. It allows Cisco customers and partners to leverage OVAL definitions and CVRF data to set up rules for the automated assessment of their own networks. It further simplifies the evaluation process and reduces the time between when a vulnerability is announced and the fix is actually implemented. That means less risk for them and their own customers tied to open vulnerabilities.
The openVuln API can be accessed via Cisco’s API Console. The console provides a simplified, guided experience through which partners and customers can obtain oAuth2 credentials and register a client application that accesses the Cisco PSIRT openVuln API. You can also access it using curl.
You can find technical details and information about the openVuln API at the new Cisco PSIRT DevNet site. We also encourage you to collaborate with others through the corresponding DevNet developer community, where users can get additional technical content, collaborate with peers, exchange sample code, and ask questions.
