- Cisco Community
- Technology and Support
- Security
- Network Security
- Re: Packet Tracer - ASA cannot ping inside to DMZ
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-26-2024 02:47 AM - edited 03-26-2024 02:49 AM
Hello Cisco Community,
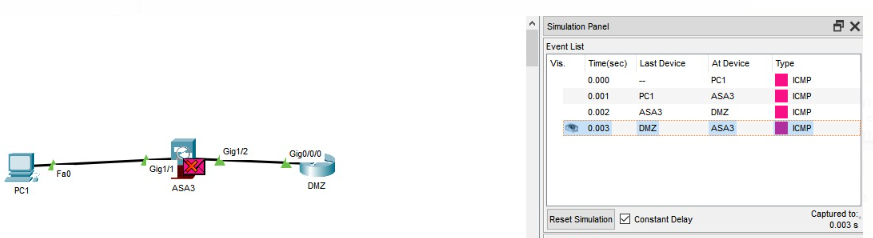
Currently i'm having problem with pinging from inside (PC) to DMZ (router dmz) through ASA. the packet always stuck at ASA when the dmz router wants to send it back. I also already configure the default route for DMZ router.
Can someone lend me a hand? I'm using ASA 5506-X and my packet tracer version is 7.3.0.0838
Here's the topology and the configuration I made:
ASA Version 9.6(1)
!
hostname ciscoasa
names
!
interface GigabitEthernet1/1
nameif inside
security-level 100
ip address 10.1.1.1 255.255.255.0
!
interface GigabitEthernet1/2
nameif dmz
security-level 50
ip address 192.168.1.1 255.255.255.0
!
interface GigabitEthernet1/3
no nameif
no security-level
no ip address
shutdown
!
interface GigabitEthernet1/4
no nameif
no security-level
no ip address
shutdown
!
interface GigabitEthernet1/5
no nameif
no security-level
no ip address
shutdown
!
interface GigabitEthernet1/6
no nameif
no security-level
no ip address
shutdown
!
interface GigabitEthernet1/7
no nameif
no security-level
no ip address
shutdown
!
interface GigabitEthernet1/8
no nameif
no security-level
no ip address
shutdown
!
interface Management1/1
management-only
no nameif
no security-level
no ip address
!
!
!
access-list inside extended permit ip any any
access-list inside extended permit icmp any any
!
!
access-group inside in interface inside
!
!
!
!
!
!
!
telnet timeout 5
ssh timeout 5
!
Solved! Go to Solution.
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-26-2024 04:00 AM
Hello @kentwirianata ,
you are missing from your ASA configuration the access-list for the DMZ:
access-list dmz extended permit icmp any any
!
access-group dmz in interface dmz
*** Please Rate All Helpful Responses ***
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-26-2024 04:00 AM
Hello @kentwirianata ,
you are missing from your ASA configuration the access-list for the DMZ:
access-list dmz extended permit icmp any any
!
access-group dmz in interface dmz
*** Please Rate All Helpful Responses ***
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-27-2024 01:52 AM
Thank you very much!!!
um..another question. If I want PC from inside can ping DMZ and got reply but from DMZ cannot ping inside, hows the ACL?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-27-2024 06:51 AM
It should work with the same access-lists. Here is the asa config from my test:
ciscoasa#show run
: Saved
:
ASA Version 9.6(1)
!
hostname ciscoasa
names
!
interface GigabitEthernet1/1
nameif inside
security-level 100
ip address 10.1.1.1 255.255.255.0
!
interface GigabitEthernet1/2
nameif dmz
security-level 50
ip address 192.168.1.1 255.255.255.0
!
interface GigabitEthernet1/3
no nameif
no security-level
no ip address
shutdown
!
interface GigabitEthernet1/4
no nameif
no security-level
no ip address
shutdown
!
interface GigabitEthernet1/5
no nameif
no security-level
no ip address
shutdown
!
interface GigabitEthernet1/6
no nameif
no security-level
no ip address
shutdown
!
interface GigabitEthernet1/7
no nameif
no security-level
no ip address
shutdown
!
interface GigabitEthernet1/8
no nameif
no security-level
no ip address
shutdown
!
interface Management1/1
management-only
no nameif
no security-level
no ip address
shutdown
!
!
!
access-list inside extended permit ip any any
access-list inside extended permit icmp any any
access-list dmz extended permit icmp any any
!
!
access-group inside in interface inside
access-group dmz in interface dmz
!
!
class-map inspection_default
match default-inspection-traffic
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect tftp
!
service-policy global_policy global
!
telnet timeout 5
ssh timeout 5
!
ciscoasa#
And the ping from the host connected in the DMZ:
Router>ping 10.1.1.2
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 10.1.1.2, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 0/0/0 ms
Router>
*** Please Rate All Helpful Responses ***
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide