- Cisco Community
- Technology and Support
- Security
- Network Access Control
- ISE Profiling without Active Auth
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
ISE Profiling without Active Auth
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-23-2017 02:06 PM
This is more of a product enhancement request or question on why ISE doesn't do this already.
ISE's profiling capabilities are great in identifying what is on your network. You can answer a lot of the "What is on my network?" question with ISE profiling without enabling active authentication (MAB or 802.1x). For example:
- As soon as I import the NAD devices into ISE with SNMP polling enabled, ISE will poll the switches and gather attached MAC addresses and gather things like CDP/LLDP information.
- If you forward DHCP requests to ISE, ISE can start to gather DHCP information.
- If ISE learns the IP of the devices it can then kick of NMAP scans for OS detection and open ports.
- If ISE learns the IP it can do a FQDN lookup on the IP.
- If ISE learns the FQDN or hostname via DHCP, it can do an AD lookup to see if that object exists in AD.
- If ISE learns SNMP is open it can SNMP scan the endpoints.
All of this can be done without having to worry about compatible IOS versions on switches. I call this ISE Lite when I talk to customers. Basically allowing me to show value, while they are upgrading their switches to compatible version and allowing me to get a jump on profiling.
The part that is frustrating is that this ISE Lite concept can't answer the "Where is the stuff plugged into my network?" question when there really is no technical reason it can't answer this. The database already has fields for NAD and NAD port so no changes would need to be made in the database. The only piece that is missing is during the SNMP poll of the NAD, ISE is not correlating the obtained MAC addresses to switch ports. All that information is available via SNMP and should be easy to correlate.
Identifying where something is plugged in without active authentication would be a huge boost to ISE. I know that doesn't consume licenses, but it shows off the power of the products.
So my question is, what am I missing here? This seems like an easy thing to add in the SNMP polling process of the NADs. Cisco Prime already does this, so the coding has already been done in the Cisco world.
Thanks.
- Labels:
-
Identity Services Engine (ISE)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-24-2017 01:34 AM
ISE will get port information without enabling dot1x or mab. You can see that in context visibility > endpoints. Just make sure that NAS-PORT-ID is selected in your columns to be viewed
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-24-2017 06:56 AM
I don't think that is true and I just retested again on 2.2 in my lab. I have my test switch defined to ISE with just SNMP enabled:
You can see the MAC addresses it learned from the switch, but no NAD name or port in Context visibility (only MACs in system are one learned from SNMP poll):
If you drill into a MAC you can see it was learned via SNMP (well now it changed to NMAP because it was scanned). It has the IP of the NAD, but ISE didn't populate the name of the NAD even though it knows it and it didn't populate the port.
Where are you seeing NAD details reported for SNMP polling?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-24-2017 11:07 AM
Please see the snapshot below from ISE.
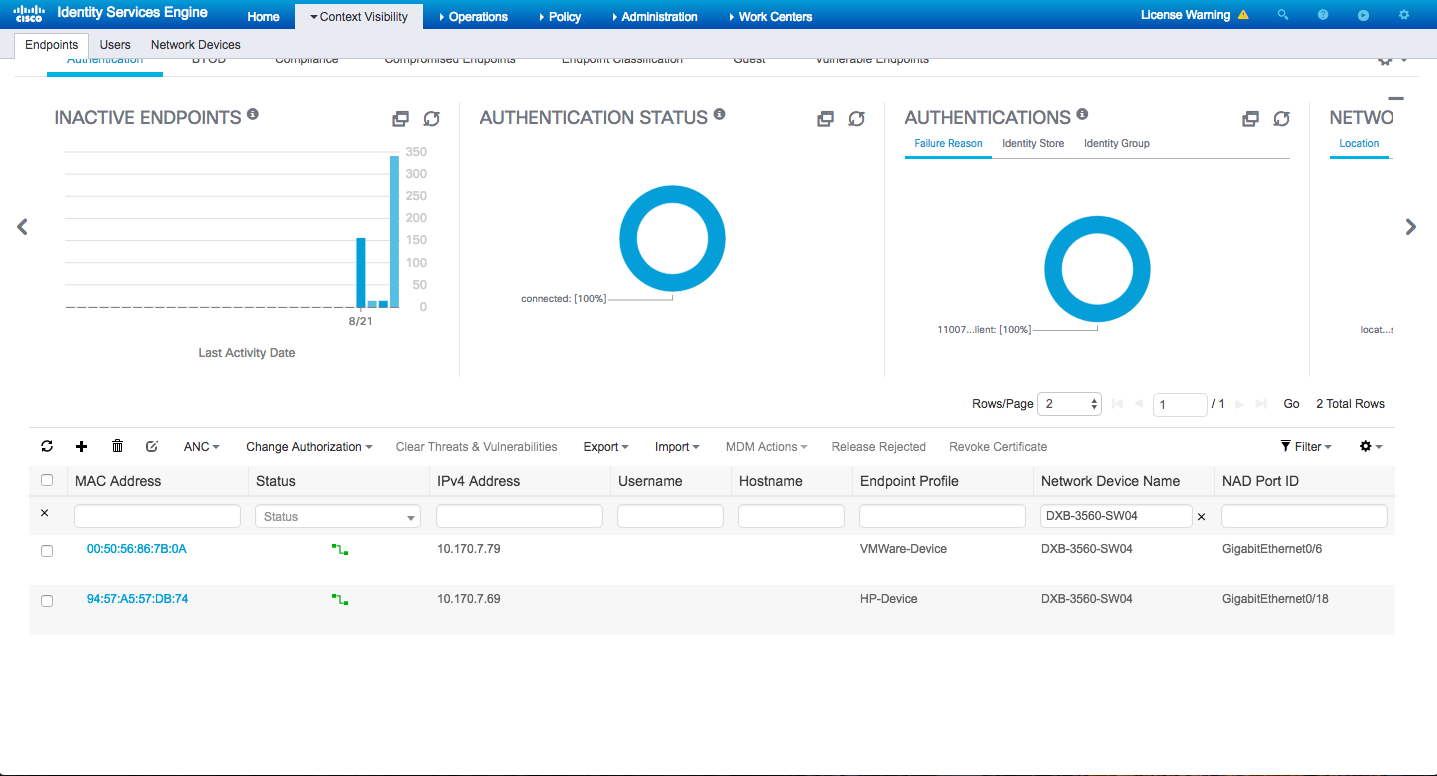
Here you see the switch isn't using mab or dot1x on the switch ports of both devices
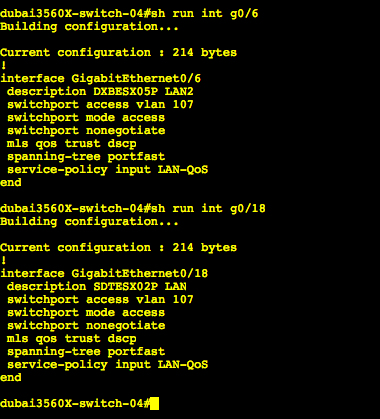
And yes the endpoint is using snmpquery probe.
Other Attributes
| 161-udp | snmp |
| 162-udp | snmptrap |
| 443-tcp | https |
| 80-tcp | http |
| AAA-Server | ########hidden####### |
| AllowedProtocolMatchedRule | dot1x |
| BYODRegistration | Unknown |
| Called-Station-ID | 7C-69-F6-7A-93-92 |
| Calling-Station-ID | 94-57-A5-57-DB-74 |
| DTLSSupport | Unknown |
| DestinationIPAddress | ######hidden###### |
| DestinationPort | 1813 |
| Device IP Address | #####hidden###### |
| Device Port | 1646 |
| Device Type | Device Type#All Device Types#SWITCHES |
| DeviceRegistrationStatus | NotRegistered |
| ElapsedDays | 43 |
| EndPointPolicy | HP-Device |
| EndPointProfilerServer | ######hidden###### |
| EndPointSource | SNMPQuery Probe |
| FailureReason | 11007 Could not locate Network Device or AAA Client |
| IPSEC | IPSEC#Is IPSEC Device#No |
| IdentityGroup | Profiled |
| InactiveDays | 0 |
| LastNmapScanTime | 2017-Jul-19 16:26:17 GST |
| Location | Location#All Locations#DXB |
| MACAddress | 94:57:A5:57:DB:74 |
| MatchedPolicy | HP-Device |
| MessageCode | 3000 |
| NADAddress | ####hidden######## |
| NAS-IP-Address | ######hidden####### |
| NAS-Port | 50018 |
| NAS-Port-Id | GigabitEthernet0/18 |
| NAS-Port-Type | Ethernet |
| Network Device Profile | Cisco |
| NetworkDeviceGroups | Location#All Locations#DXB, Device Type#All Device Types#SWITCHES, IPSEC#Is IPSEC Device#No |
| NetworkDeviceName | DXB-3560-SW04 |
| NmapScanCount | 3 |
| OUI | Hewlett Packard |
| PolicyVersion | 56 |
| PostureApplicable | Yes |
| SelectedAccessService | Default Network Access |
| Service-Type | Framed |
| StaticAssignment | false |
| StaticGroupAssignment | false |
| Total Certainty Factor | 10 |
| dot1xAuthAuthControlledPortControl | 2 |
| dot1xAuthAuthControlledPortStatus | 2 |
| ifDescr | GigabitEthernet0/18 |
| ifIndex | 10118 |
| ifOperStatus | 1 |
| ip | ####hidden###### |
| operating-system | VMware ESXi 5.1 (accuracy 98%) |
| operating-system-result | VMware ESXi 5.1 (accuracy 98%) |
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-24-2017 11:22 AM
What version are you running? Trying to figure why you are seeing something different.
You deleted all your endpoint from the Context Visibility and had them pulled in from just SNMP? I am running a 3560 as my lab switch. I see you are running 3650. I can’t see how that would matter but who knows.
Do you have SNMP traps or syslog enabled on your switch pointing at ISE?
Paul Haferman
Office- 920.996.3011
Cell- 920.284.9250
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-24-2017 12:20 PM
Also it appears you have done authentication at one time on these MAC addresses. The one you show below has “Allowed Protocol Match Rule” set to “dot1x” which would not be set if you only did SNMP polling no active auth.
Like I said before completely delete all your endpoints, turn on only SNMP polling on the NAD, no syslog or SNMP traps to ISE and see what you get.
Paul Haferman
Office- 920.996.3011
Cell- 920.284.9250
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-06-2017 02:21 AM
Sorry for later response. I was waiting for new installation. This is out of default installation.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-06-2017 05:47 AM
Yes but the default rule set authenticated almost anything. Click on the ones that have ports shown and you will see active authentication. Turn off all RADIUS authentication on your network devices and do only SNMP queries. That was the original question.
Paul Haferman
Office- 920.996.3011
Cell- 920.284.9250
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-17-2023 03:51 AM
has this feature been implemented?
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide

