- Cisco Community
- Technology and Support
- Security
- VPN
- Cisco Firepower Access remote site-to-site subnet via Cisco Anyconnect
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-11-2024 06:14 AM
When a client connect to the HQ via AnyConnect vpn, they can access the HQ local subnet, but can´t access the subnet at the remote office, that has an site-to-site connection to the HQ.
Can this be configuret via the Cisco Firepower gui?
Cisco Firepower 1120
Solved! Go to Solution.
- Labels:
-
AnyConnect
-
Remote Access
-
VPN
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-17-2024 03:20 PM
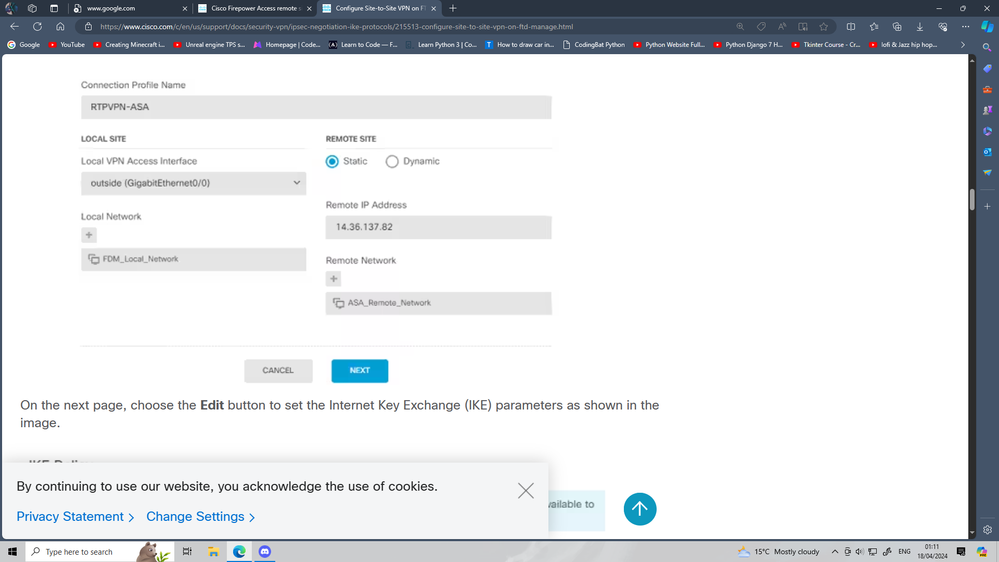
Configure Site-to-Site VPN on FTD Managed by FDM - Cisco
this guide to config IPsec in FDM
first step is add VPN subnet to IPSec
A-Objects > Networks > Add New Network
B-then in local network add network we config in sub step A
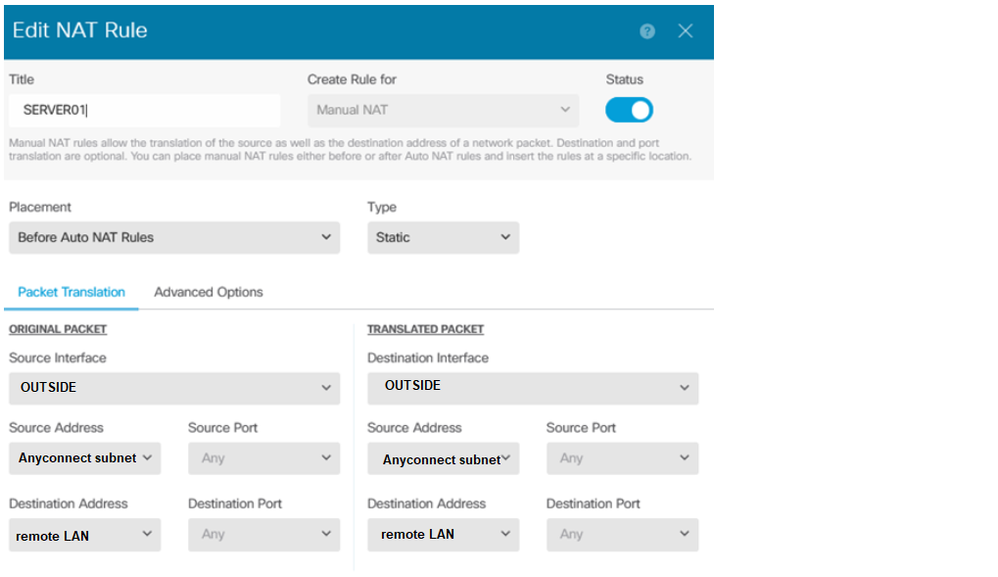
second step config out,out NAT
NOTE:- the Anyconnect subnet must also need to add in peer ACL
MHM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-11-2024 06:28 AM
Add Anyconnect VPN subnet to ACL of IPSec S2S
Add no-NAT from your anyconnect subnet to remote LAN and interface will be outside'outside.
Try above two steps and check
MHM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-11-2024 06:38 AM
How can this be done via the gui?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-11-2024 06:45 AM
You meaning FDM ?
MHM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-11-2024 06:48 AM
Yes i mean FDM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-12-2024 04:49 AM
Do you have an idea, how this can be done?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-12-2024 05:27 AM
Share the config of ipsec vpn in fdm
MHM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-16-2024 04:58 AM
It should be in Policy > NAT section. Also, please note that you would need to configure the remote site to send the traffic destined to AnyConnect subnet over the site-to-site VPN tunnel and it also needs to be exempted from NAT.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-16-2024 05:28 AM
At the remote site, we use a Meraki MX67
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-16-2024 06:20 AM - edited 04-16-2024 06:21 AM
Ok, then you would need to add the AnyConnect subnet to the VPN subnets list in Meraki dashboard.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-15-2024 12:39 AM
Thank you for you help
Connection Name: AAHQ-BRANCH1
Type: Policy Based
VPN Access Interfaces: outside (92.246.12.1xx)
Network: AA_Network(192.68.134.0/24)
Peer IP Address: 95.138.217.xx
Peer Network: Branch1_Network(192.168.130.0/24)
IKE Version 2: Disabled
IKE Version 1
IKE Policy: aes-256-pre-share-sha-14
IPSec Proposal: esp-aes-256-esp-sha-hmac-tunnel
Authentication Type: Pre-shared Manual Key
IPSec Settings
Lifetime Duration: 28800 seconds
Lifetime Size: 4608000 kilobytes
Additional Options
NAT Exempt: inside (192.68.134.1)
Diffie-Hellman Group: Null (not selected)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-16-2024 04:38 AM
Do you need more from the configuration?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-17-2024 03:20 PM
Configure Site-to-Site VPN on FTD Managed by FDM - Cisco
this guide to config IPsec in FDM
first step is add VPN subnet to IPSec
A-Objects > Networks > Add New Network
B-then in local network add network we config in sub step A
second step config out,out NAT
NOTE:- the Anyconnect subnet must also need to add in peer ACL
MHM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-18-2024 06:43 AM
Thank you MHM
I was missing the Anyconnect network at the local network.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide