Trending Topics
Cisco Community is an active and collaborative place to learn more about our products and ask questions of peers and Cisco experts! Check out some of the most popular conversations happening right now!
-
Ask Me Anything - Drive to 15X
by Brooke Hammer -
Cisco 1010 ports not coming back on after reboot
by taitas -
ASA dropping Azure Traffic manager http health probes
by mmjcollett -
LoadBalancing on viosl2
by geppone -
[注意喚起]ISE 3.2でのconfiguration backupのrestoreに関して その2
by maarai -
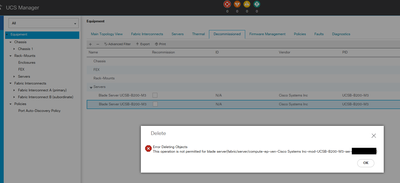
[UCS] 互換性確認ツールの使用方法
by yusnakan -
NAD config for 802.1x/MAB with ISE
by babalao -
CDP Mismatch from CDP: Why?
by Chris Schroeder